mirror of
https://github.com/go-gitea/gitea
synced 2025-11-02 20:38:26 +00:00
Add user blocking (#29028)
Fixes #17453 This PR adds the abbility to block a user from a personal account or organization to restrict how the blocked user can interact with the blocker. The docs explain what's the consequence of blocking a user. Screenshots: 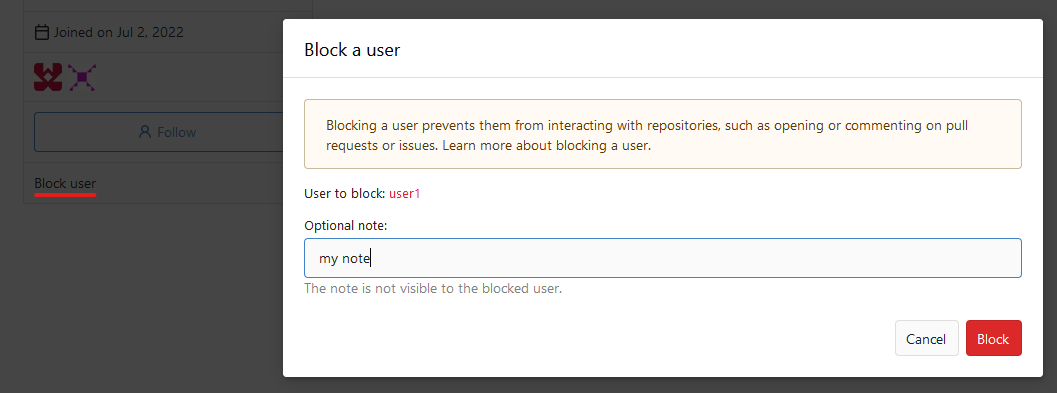 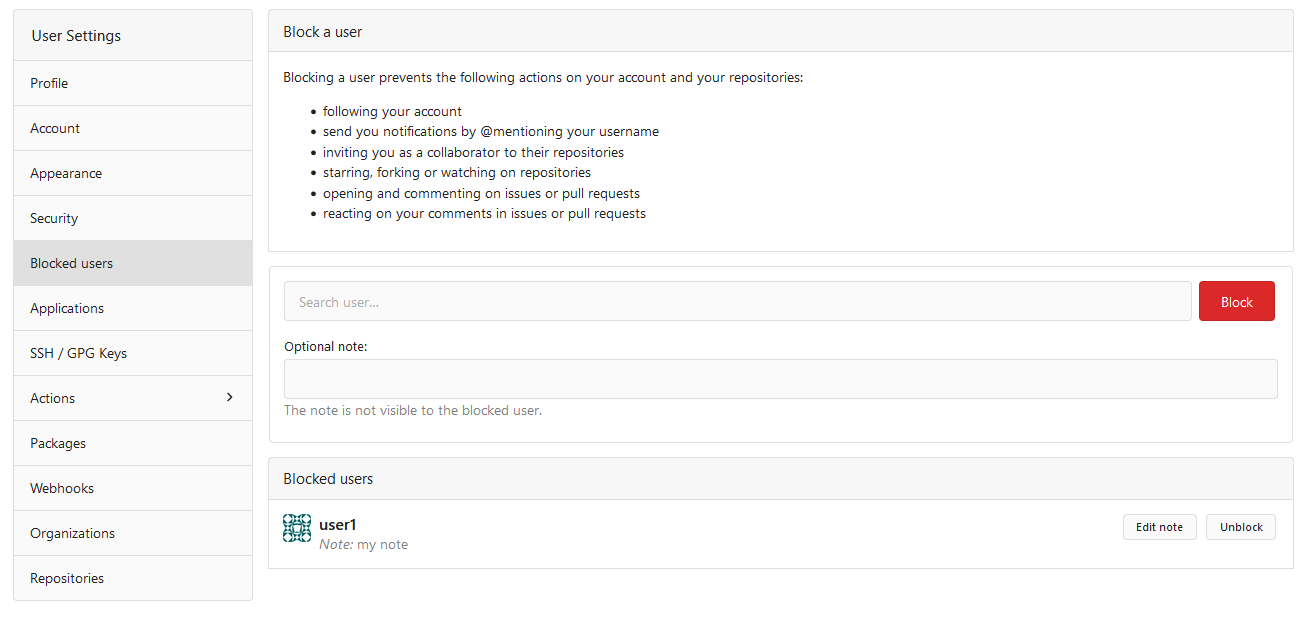  --------- Co-authored-by: Lauris BH <lauris@nix.lv>
This commit is contained in:
@@ -108,6 +108,32 @@ func TestAPICreateComment(t *testing.T) {
|
||||
DecodeJSON(t, resp, &updatedComment)
|
||||
assert.EqualValues(t, commentBody, updatedComment.Body)
|
||||
unittest.AssertExistsAndLoadBean(t, &issues_model.Comment{ID: updatedComment.ID, IssueID: issue.ID, Content: commentBody})
|
||||
|
||||
t.Run("BlockedByRepoOwner", func(t *testing.T) {
|
||||
defer tests.PrintCurrentTest(t)()
|
||||
|
||||
user34 := unittest.AssertExistsAndLoadBean(t, &user_model.User{ID: 34})
|
||||
issue := unittest.AssertExistsAndLoadBean(t, &issues_model.Issue{ID: 1})
|
||||
repo := unittest.AssertExistsAndLoadBean(t, &repo_model.Repository{ID: issue.RepoID})
|
||||
|
||||
req := NewRequestWithValues(t, "POST", fmt.Sprintf("/api/v1/repos/%s/%s/issues/%d/comments", repo.OwnerName, repo.Name, issue.Index), map[string]string{
|
||||
"body": commentBody,
|
||||
}).AddTokenAuth(getUserToken(t, user34.Name, auth_model.AccessTokenScopeWriteRepository))
|
||||
MakeRequest(t, req, http.StatusForbidden)
|
||||
})
|
||||
|
||||
t.Run("BlockedByIssuePoster", func(t *testing.T) {
|
||||
defer tests.PrintCurrentTest(t)()
|
||||
|
||||
user34 := unittest.AssertExistsAndLoadBean(t, &user_model.User{ID: 34})
|
||||
issue := unittest.AssertExistsAndLoadBean(t, &issues_model.Issue{ID: 13})
|
||||
repo := unittest.AssertExistsAndLoadBean(t, &repo_model.Repository{ID: issue.RepoID})
|
||||
|
||||
req := NewRequestWithValues(t, "POST", fmt.Sprintf("/api/v1/repos/%s/%s/issues/%d/comments", repo.OwnerName, repo.Name, issue.Index), map[string]string{
|
||||
"body": commentBody,
|
||||
}).AddTokenAuth(getUserToken(t, user34.Name, auth_model.AccessTokenScopeWriteRepository))
|
||||
MakeRequest(t, req, http.StatusForbidden)
|
||||
})
|
||||
}
|
||||
|
||||
func TestAPIGetComment(t *testing.T) {
|
||||
|
||||
@@ -58,6 +58,13 @@ func TestAPIIssuesReactions(t *testing.T) {
|
||||
// Add existing reaction
|
||||
MakeRequest(t, req, http.StatusForbidden)
|
||||
|
||||
// Blocked user can't react to comment
|
||||
user34 := unittest.AssertExistsAndLoadBean(t, &user_model.User{ID: 34})
|
||||
req = NewRequestWithJSON(t, "POST", urlStr, &api.EditReactionOption{
|
||||
Reaction: "rocket",
|
||||
}).AddTokenAuth(getUserToken(t, user34.Name, auth_model.AccessTokenScopeWriteIssue))
|
||||
MakeRequest(t, req, http.StatusForbidden)
|
||||
|
||||
// Get end result of reaction list of issue #1
|
||||
req = NewRequest(t, "GET", urlStr).
|
||||
AddTokenAuth(token)
|
||||
|
||||
@@ -84,7 +84,7 @@ func TestAPICreateIssue(t *testing.T) {
|
||||
|
||||
session := loginUser(t, owner.Name)
|
||||
token := getTokenForLoggedInUser(t, session, auth_model.AccessTokenScopeWriteIssue)
|
||||
urlStr := fmt.Sprintf("/api/v1/repos/%s/%s/issues?state=all", owner.Name, repoBefore.Name)
|
||||
urlStr := fmt.Sprintf("/api/v1/repos/%s/%s/issues", owner.Name, repoBefore.Name)
|
||||
req := NewRequestWithJSON(t, "POST", urlStr, &api.CreateIssueOption{
|
||||
Body: body,
|
||||
Title: title,
|
||||
@@ -106,6 +106,12 @@ func TestAPICreateIssue(t *testing.T) {
|
||||
repoAfter := unittest.AssertExistsAndLoadBean(t, &repo_model.Repository{ID: 1})
|
||||
assert.Equal(t, repoBefore.NumIssues+1, repoAfter.NumIssues)
|
||||
assert.Equal(t, repoBefore.NumClosedIssues, repoAfter.NumClosedIssues)
|
||||
|
||||
user34 := unittest.AssertExistsAndLoadBean(t, &user_model.User{ID: 34})
|
||||
req = NewRequestWithJSON(t, "POST", urlStr, &api.CreateIssueOption{
|
||||
Title: title,
|
||||
}).AddTokenAuth(getUserToken(t, user34.Name, auth_model.AccessTokenScopeWriteIssue))
|
||||
MakeRequest(t, req, http.StatusForbidden)
|
||||
}
|
||||
|
||||
func TestAPICreateIssueParallel(t *testing.T) {
|
||||
@@ -117,7 +123,7 @@ func TestAPICreateIssueParallel(t *testing.T) {
|
||||
|
||||
session := loginUser(t, owner.Name)
|
||||
token := getTokenForLoggedInUser(t, session, auth_model.AccessTokenScopeWriteIssue)
|
||||
urlStr := fmt.Sprintf("/api/v1/repos/%s/%s/issues?state=all", owner.Name, repoBefore.Name)
|
||||
urlStr := fmt.Sprintf("/api/v1/repos/%s/%s/issues", owner.Name, repoBefore.Name)
|
||||
|
||||
var wg sync.WaitGroup
|
||||
for i := 0; i < 10; i++ {
|
||||
|
||||
@@ -27,6 +27,7 @@ func TestAPIRepoCollaboratorPermission(t *testing.T) {
|
||||
user5 := unittest.AssertExistsAndLoadBean(t, &user_model.User{ID: 5})
|
||||
user10 := unittest.AssertExistsAndLoadBean(t, &user_model.User{ID: 10})
|
||||
user11 := unittest.AssertExistsAndLoadBean(t, &user_model.User{ID: 11})
|
||||
user34 := unittest.AssertExistsAndLoadBean(t, &user_model.User{ID: 34})
|
||||
|
||||
testCtx := NewAPITestContext(t, repo2Owner.Name, repo2.Name, auth_model.AccessTokenScopeWriteRepository)
|
||||
|
||||
@@ -86,6 +87,12 @@ func TestAPIRepoCollaboratorPermission(t *testing.T) {
|
||||
MakeRequest(t, req, http.StatusNotFound)
|
||||
})
|
||||
|
||||
t.Run("CollaboratorBlocked", func(t *testing.T) {
|
||||
ctx := NewAPITestContext(t, repo2Owner.Name, repo2.Name, auth_model.AccessTokenScopeWriteRepository)
|
||||
ctx.ExpectedCode = http.StatusForbidden
|
||||
doAPIAddCollaborator(ctx, user34.Name, perm.AccessModeAdmin)(t)
|
||||
})
|
||||
|
||||
t.Run("CollaboratorCanQueryItsPermissions", func(t *testing.T) {
|
||||
t.Run("AddUserAsCollaboratorWithReadAccess", doAPIAddCollaborator(testCtx, user5.Name, perm.AccessModeRead))
|
||||
|
||||
|
||||
243
tests/integration/api_user_block_test.go
Normal file
243
tests/integration/api_user_block_test.go
Normal file
@@ -0,0 +1,243 @@
|
||||
// Copyright 2024 The Gitea Authors. All rights reserved.
|
||||
// SPDX-License-Identifier: MIT
|
||||
|
||||
package integration
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
"net/http"
|
||||
"testing"
|
||||
|
||||
"code.gitea.io/gitea/models"
|
||||
auth_model "code.gitea.io/gitea/models/auth"
|
||||
"code.gitea.io/gitea/models/db"
|
||||
issues_model "code.gitea.io/gitea/models/issues"
|
||||
repo_model "code.gitea.io/gitea/models/repo"
|
||||
api "code.gitea.io/gitea/modules/structs"
|
||||
"code.gitea.io/gitea/tests"
|
||||
|
||||
"github.com/stretchr/testify/assert"
|
||||
)
|
||||
|
||||
func TestBlockUser(t *testing.T) {
|
||||
defer tests.PrepareTestEnv(t)()
|
||||
|
||||
countStars := func(t *testing.T, repoOwnerID, starrerID int64) int64 {
|
||||
count, err := db.Count[repo_model.Repository](db.DefaultContext, &repo_model.StarredReposOptions{
|
||||
StarrerID: starrerID,
|
||||
RepoOwnerID: repoOwnerID,
|
||||
IncludePrivate: true,
|
||||
})
|
||||
assert.NoError(t, err)
|
||||
return count
|
||||
}
|
||||
|
||||
countWatches := func(t *testing.T, repoOwnerID, watcherID int64) int64 {
|
||||
count, err := db.Count[repo_model.Repository](db.DefaultContext, &repo_model.WatchedReposOptions{
|
||||
WatcherID: watcherID,
|
||||
RepoOwnerID: repoOwnerID,
|
||||
})
|
||||
assert.NoError(t, err)
|
||||
return count
|
||||
}
|
||||
|
||||
countRepositoryTransfers := func(t *testing.T, senderID, recipientID int64) int64 {
|
||||
transfers, err := models.GetPendingRepositoryTransfers(db.DefaultContext, &models.PendingRepositoryTransferOptions{
|
||||
SenderID: senderID,
|
||||
RecipientID: recipientID,
|
||||
})
|
||||
assert.NoError(t, err)
|
||||
return int64(len(transfers))
|
||||
}
|
||||
|
||||
countAssignedIssues := func(t *testing.T, repoOwnerID, assigneeID int64) int64 {
|
||||
_, count, err := issues_model.GetAssignedIssues(db.DefaultContext, &issues_model.AssignedIssuesOptions{
|
||||
AssigneeID: assigneeID,
|
||||
RepoOwnerID: repoOwnerID,
|
||||
})
|
||||
assert.NoError(t, err)
|
||||
return count
|
||||
}
|
||||
|
||||
countCollaborations := func(t *testing.T, repoOwnerID, collaboratorID int64) int64 {
|
||||
count, err := db.Count[repo_model.Collaboration](db.DefaultContext, &repo_model.FindCollaborationOptions{
|
||||
CollaboratorID: collaboratorID,
|
||||
RepoOwnerID: repoOwnerID,
|
||||
})
|
||||
assert.NoError(t, err)
|
||||
return count
|
||||
}
|
||||
|
||||
t.Run("User", func(t *testing.T) {
|
||||
var blockerID int64 = 16
|
||||
blockerName := "user16"
|
||||
blockerToken := getUserToken(t, blockerName, auth_model.AccessTokenScopeWriteUser)
|
||||
|
||||
var blockeeID int64 = 10
|
||||
blockeeName := "user10"
|
||||
|
||||
t.Run("Block", func(t *testing.T) {
|
||||
req := NewRequest(t, "PUT", fmt.Sprintf("/api/v1/user/blocks/%s", blockeeName))
|
||||
MakeRequest(t, req, http.StatusUnauthorized)
|
||||
|
||||
assert.EqualValues(t, 1, countStars(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 1, countWatches(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 1, countRepositoryTransfers(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 1, countCollaborations(t, blockerID, blockeeID))
|
||||
|
||||
req = NewRequest(t, "GET", fmt.Sprintf("/api/v1/user/blocks/%s", blockeeName)).
|
||||
AddTokenAuth(blockerToken)
|
||||
MakeRequest(t, req, http.StatusNotFound)
|
||||
|
||||
req = NewRequest(t, "PUT", fmt.Sprintf("/api/v1/user/blocks/%s?reason=test", blockeeName)).
|
||||
AddTokenAuth(blockerToken)
|
||||
MakeRequest(t, req, http.StatusNoContent)
|
||||
|
||||
assert.EqualValues(t, 0, countStars(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 0, countWatches(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 0, countRepositoryTransfers(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 0, countCollaborations(t, blockerID, blockeeID))
|
||||
|
||||
req = NewRequest(t, "GET", fmt.Sprintf("/api/v1/user/blocks/%s", blockeeName)).
|
||||
AddTokenAuth(blockerToken)
|
||||
MakeRequest(t, req, http.StatusNoContent)
|
||||
|
||||
req = NewRequest(t, "PUT", fmt.Sprintf("/api/v1/user/blocks/%s", blockeeName)).
|
||||
AddTokenAuth(blockerToken)
|
||||
MakeRequest(t, req, http.StatusBadRequest) // can't block blocked user
|
||||
|
||||
req = NewRequest(t, "PUT", fmt.Sprintf("/api/v1/user/blocks/%s", "org3")).
|
||||
AddTokenAuth(blockerToken)
|
||||
MakeRequest(t, req, http.StatusBadRequest) // can't block organization
|
||||
|
||||
req = NewRequest(t, "GET", "/api/v1/user/blocks")
|
||||
MakeRequest(t, req, http.StatusUnauthorized)
|
||||
|
||||
req = NewRequest(t, "GET", "/api/v1/user/blocks").
|
||||
AddTokenAuth(blockerToken)
|
||||
resp := MakeRequest(t, req, http.StatusOK)
|
||||
|
||||
var users []api.User
|
||||
DecodeJSON(t, resp, &users)
|
||||
|
||||
assert.Len(t, users, 1)
|
||||
assert.Equal(t, blockeeName, users[0].UserName)
|
||||
})
|
||||
|
||||
t.Run("Unblock", func(t *testing.T) {
|
||||
req := NewRequest(t, "DELETE", fmt.Sprintf("/api/v1/user/blocks/%s", blockeeName))
|
||||
MakeRequest(t, req, http.StatusUnauthorized)
|
||||
|
||||
req = NewRequest(t, "DELETE", fmt.Sprintf("/api/v1/user/blocks/%s", blockeeName)).
|
||||
AddTokenAuth(blockerToken)
|
||||
MakeRequest(t, req, http.StatusNoContent)
|
||||
|
||||
req = NewRequest(t, "DELETE", fmt.Sprintf("/api/v1/user/blocks/%s", blockeeName)).
|
||||
AddTokenAuth(blockerToken)
|
||||
MakeRequest(t, req, http.StatusBadRequest)
|
||||
|
||||
req = NewRequest(t, "DELETE", fmt.Sprintf("/api/v1/user/blocks/%s", "org3")).
|
||||
AddTokenAuth(blockerToken)
|
||||
MakeRequest(t, req, http.StatusBadRequest)
|
||||
|
||||
req = NewRequest(t, "GET", "/api/v1/user/blocks").
|
||||
AddTokenAuth(blockerToken)
|
||||
resp := MakeRequest(t, req, http.StatusOK)
|
||||
|
||||
var users []api.User
|
||||
DecodeJSON(t, resp, &users)
|
||||
|
||||
assert.Empty(t, users)
|
||||
})
|
||||
})
|
||||
|
||||
t.Run("Organization", func(t *testing.T) {
|
||||
var blockerID int64 = 3
|
||||
blockerName := "org3"
|
||||
|
||||
doerToken := getUserToken(t, "user2", auth_model.AccessTokenScopeWriteUser, auth_model.AccessTokenScopeWriteOrganization)
|
||||
|
||||
var blockeeID int64 = 10
|
||||
blockeeName := "user10"
|
||||
|
||||
t.Run("Block", func(t *testing.T) {
|
||||
req := NewRequest(t, "PUT", fmt.Sprintf("/api/v1/orgs/%s/blocks/%s", blockerName, blockeeName))
|
||||
MakeRequest(t, req, http.StatusUnauthorized)
|
||||
|
||||
req = NewRequest(t, "PUT", fmt.Sprintf("/api/v1/orgs/%s/blocks/%s", blockerName, "user4")).
|
||||
AddTokenAuth(doerToken)
|
||||
MakeRequest(t, req, http.StatusBadRequest) // can't block member
|
||||
|
||||
assert.EqualValues(t, 1, countStars(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 1, countWatches(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 1, countRepositoryTransfers(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 1, countAssignedIssues(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 1, countCollaborations(t, blockerID, blockeeID))
|
||||
|
||||
req = NewRequest(t, "GET", fmt.Sprintf("/api/v1/orgs/%s/blocks/%s", blockerName, blockeeName)).
|
||||
AddTokenAuth(doerToken)
|
||||
MakeRequest(t, req, http.StatusNotFound)
|
||||
|
||||
req = NewRequest(t, "PUT", fmt.Sprintf("/api/v1/orgs/%s/blocks/%s?reason=test", blockerName, blockeeName)).
|
||||
AddTokenAuth(doerToken)
|
||||
MakeRequest(t, req, http.StatusNoContent)
|
||||
|
||||
assert.EqualValues(t, 0, countStars(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 0, countWatches(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 0, countRepositoryTransfers(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 0, countAssignedIssues(t, blockerID, blockeeID))
|
||||
assert.EqualValues(t, 0, countCollaborations(t, blockerID, blockeeID))
|
||||
|
||||
req = NewRequest(t, "GET", fmt.Sprintf("/api/v1/orgs/%s/blocks/%s", blockerName, blockeeName)).
|
||||
AddTokenAuth(doerToken)
|
||||
MakeRequest(t, req, http.StatusNoContent)
|
||||
|
||||
req = NewRequest(t, "PUT", fmt.Sprintf("/api/v1/orgs/%s/blocks/%s", blockerName, blockeeName)).
|
||||
AddTokenAuth(doerToken)
|
||||
MakeRequest(t, req, http.StatusBadRequest) // can't block blocked user
|
||||
|
||||
req = NewRequest(t, "PUT", fmt.Sprintf("/api/v1/orgs/%s/blocks/%s", blockerName, "org3")).
|
||||
AddTokenAuth(doerToken)
|
||||
MakeRequest(t, req, http.StatusBadRequest) // can't block organization
|
||||
|
||||
req = NewRequest(t, "GET", fmt.Sprintf("/api/v1/orgs/%s/blocks", blockerName))
|
||||
MakeRequest(t, req, http.StatusUnauthorized)
|
||||
|
||||
req = NewRequest(t, "GET", fmt.Sprintf("/api/v1/orgs/%s/blocks", blockerName)).
|
||||
AddTokenAuth(doerToken)
|
||||
resp := MakeRequest(t, req, http.StatusOK)
|
||||
|
||||
var users []api.User
|
||||
DecodeJSON(t, resp, &users)
|
||||
|
||||
assert.Len(t, users, 1)
|
||||
assert.Equal(t, blockeeName, users[0].UserName)
|
||||
})
|
||||
|
||||
t.Run("Unblock", func(t *testing.T) {
|
||||
req := NewRequest(t, "DELETE", fmt.Sprintf("/api/v1/orgs/%s/blocks/%s", blockerName, blockeeName))
|
||||
MakeRequest(t, req, http.StatusUnauthorized)
|
||||
|
||||
req = NewRequest(t, "DELETE", fmt.Sprintf("/api/v1/orgs/%s/blocks/%s", blockerName, blockeeName)).
|
||||
AddTokenAuth(doerToken)
|
||||
MakeRequest(t, req, http.StatusNoContent)
|
||||
|
||||
req = NewRequest(t, "DELETE", fmt.Sprintf("/api/v1/orgs/%s/blocks/%s", blockerName, blockeeName)).
|
||||
AddTokenAuth(doerToken)
|
||||
MakeRequest(t, req, http.StatusBadRequest)
|
||||
|
||||
req = NewRequest(t, "DELETE", fmt.Sprintf("/api/v1/orgs/%s/blocks/%s", blockerName, "org3")).
|
||||
AddTokenAuth(doerToken)
|
||||
MakeRequest(t, req, http.StatusBadRequest)
|
||||
|
||||
req = NewRequest(t, "GET", fmt.Sprintf("/api/v1/orgs/%s/blocks", blockerName)).
|
||||
AddTokenAuth(doerToken)
|
||||
resp := MakeRequest(t, req, http.StatusOK)
|
||||
|
||||
var users []api.User
|
||||
DecodeJSON(t, resp, &users)
|
||||
|
||||
assert.Empty(t, users)
|
||||
})
|
||||
})
|
||||
}
|
||||
@@ -9,6 +9,8 @@ import (
|
||||
"testing"
|
||||
|
||||
auth_model "code.gitea.io/gitea/models/auth"
|
||||
"code.gitea.io/gitea/models/unittest"
|
||||
user_model "code.gitea.io/gitea/models/user"
|
||||
api "code.gitea.io/gitea/modules/structs"
|
||||
"code.gitea.io/gitea/tests"
|
||||
|
||||
@@ -33,6 +35,12 @@ func TestAPIFollow(t *testing.T) {
|
||||
req := NewRequest(t, "PUT", fmt.Sprintf("/api/v1/user/following/%s", user1)).
|
||||
AddTokenAuth(token2)
|
||||
MakeRequest(t, req, http.StatusNoContent)
|
||||
|
||||
// blocked user can't follow blocker
|
||||
user34 := unittest.AssertExistsAndLoadBean(t, &user_model.User{ID: 34})
|
||||
req = NewRequest(t, "PUT", "/api/v1/user/following/user2").
|
||||
AddTokenAuth(getUserToken(t, user34.Name, auth_model.AccessTokenScopeWriteUser))
|
||||
MakeRequest(t, req, http.StatusForbidden)
|
||||
})
|
||||
|
||||
t.Run("ListFollowing", func(t *testing.T) {
|
||||
|
||||
@@ -9,6 +9,8 @@ import (
|
||||
"testing"
|
||||
|
||||
auth_model "code.gitea.io/gitea/models/auth"
|
||||
"code.gitea.io/gitea/models/unittest"
|
||||
user_model "code.gitea.io/gitea/models/user"
|
||||
api "code.gitea.io/gitea/modules/structs"
|
||||
"code.gitea.io/gitea/tests"
|
||||
|
||||
@@ -31,6 +33,12 @@ func TestAPIStar(t *testing.T) {
|
||||
req := NewRequest(t, "PUT", fmt.Sprintf("/api/v1/user/starred/%s", repo)).
|
||||
AddTokenAuth(tokenWithUserScope)
|
||||
MakeRequest(t, req, http.StatusNoContent)
|
||||
|
||||
// blocked user can't star a repo
|
||||
user34 := unittest.AssertExistsAndLoadBean(t, &user_model.User{ID: 34})
|
||||
req = NewRequest(t, "PUT", fmt.Sprintf("/api/v1/user/starred/%s", repo)).
|
||||
AddTokenAuth(getUserToken(t, user34.Name, auth_model.AccessTokenScopeWriteRepository))
|
||||
MakeRequest(t, req, http.StatusForbidden)
|
||||
})
|
||||
|
||||
t.Run("GetStarredRepos", func(t *testing.T) {
|
||||
|
||||
@@ -9,6 +9,8 @@ import (
|
||||
"testing"
|
||||
|
||||
auth_model "code.gitea.io/gitea/models/auth"
|
||||
"code.gitea.io/gitea/models/unittest"
|
||||
user_model "code.gitea.io/gitea/models/user"
|
||||
api "code.gitea.io/gitea/modules/structs"
|
||||
"code.gitea.io/gitea/tests"
|
||||
|
||||
@@ -31,6 +33,12 @@ func TestAPIWatch(t *testing.T) {
|
||||
req := NewRequest(t, "PUT", fmt.Sprintf("/api/v1/repos/%s/subscription", repo)).
|
||||
AddTokenAuth(tokenWithRepoScope)
|
||||
MakeRequest(t, req, http.StatusOK)
|
||||
|
||||
// blocked user can't watch a repo
|
||||
user34 := unittest.AssertExistsAndLoadBean(t, &user_model.User{ID: 34})
|
||||
req = NewRequest(t, "PUT", fmt.Sprintf("/api/v1/repos/%s/subscription", repo)).
|
||||
AddTokenAuth(getUserToken(t, user34.Name, auth_model.AccessTokenScopeWriteRepository))
|
||||
MakeRequest(t, req, http.StatusForbidden)
|
||||
})
|
||||
|
||||
t.Run("GetWatchedRepos", func(t *testing.T) {
|
||||
|
||||
@@ -428,9 +428,9 @@ func TestLDAPGroupTeamSyncAddMember(t *testing.T) {
|
||||
isMember, err := organization.IsTeamMember(db.DefaultContext, usersOrgs[0].ID, team.ID, user.ID)
|
||||
assert.NoError(t, err)
|
||||
assert.True(t, isMember, "Membership should be added to the right team")
|
||||
err = models.RemoveTeamMember(db.DefaultContext, team, user.ID)
|
||||
err = models.RemoveTeamMember(db.DefaultContext, team, user)
|
||||
assert.NoError(t, err)
|
||||
err = models.RemoveOrgUser(db.DefaultContext, usersOrgs[0].ID, user.ID)
|
||||
err = models.RemoveOrgUser(db.DefaultContext, usersOrgs[0], user)
|
||||
assert.NoError(t, err)
|
||||
} else {
|
||||
// assert members of LDAP group "cn=admin_staff" keep initial team membership since mapped team does not exist
|
||||
@@ -460,7 +460,7 @@ func TestLDAPGroupTeamSyncRemoveMember(t *testing.T) {
|
||||
})
|
||||
err = organization.AddOrgUser(db.DefaultContext, org.ID, user.ID)
|
||||
assert.NoError(t, err)
|
||||
err = models.AddTeamMember(db.DefaultContext, team, user.ID)
|
||||
err = models.AddTeamMember(db.DefaultContext, team, user)
|
||||
assert.NoError(t, err)
|
||||
isMember, err := organization.IsOrganizationMember(db.DefaultContext, org.ID, user.ID)
|
||||
assert.NoError(t, err)
|
||||
|
||||
Reference in New Issue
Block a user