mirror of
https://github.com/go-gitea/gitea
synced 2024-07-02 16:15:47 +00:00
Co-Author: @silverwind @wxiaoguang Replace: #24404 See: - [defining configuration variables for multiple workflows](https://docs.github.com/en/actions/learn-github-actions/variables#defining-configuration-variables-for-multiple-workflows) - [vars context](https://docs.github.com/en/actions/learn-github-actions/contexts#vars-context) Related to: - [x] protocol: https://gitea.com/gitea/actions-proto-def/pulls/7 - [x] act_runner: https://gitea.com/gitea/act_runner/pulls/157 - [x] act: https://gitea.com/gitea/act/pulls/43 #### Screenshoot Create Variable: 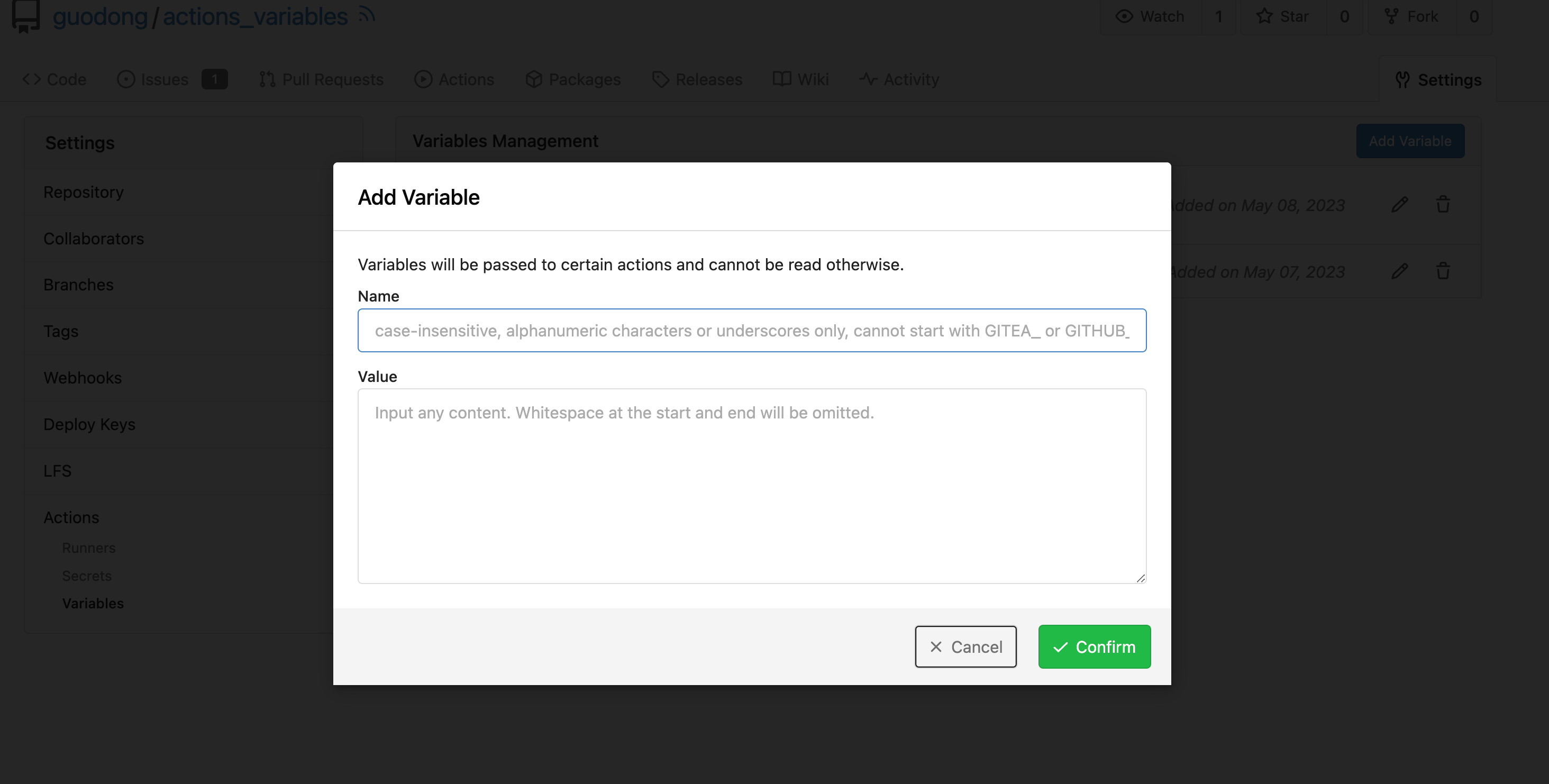 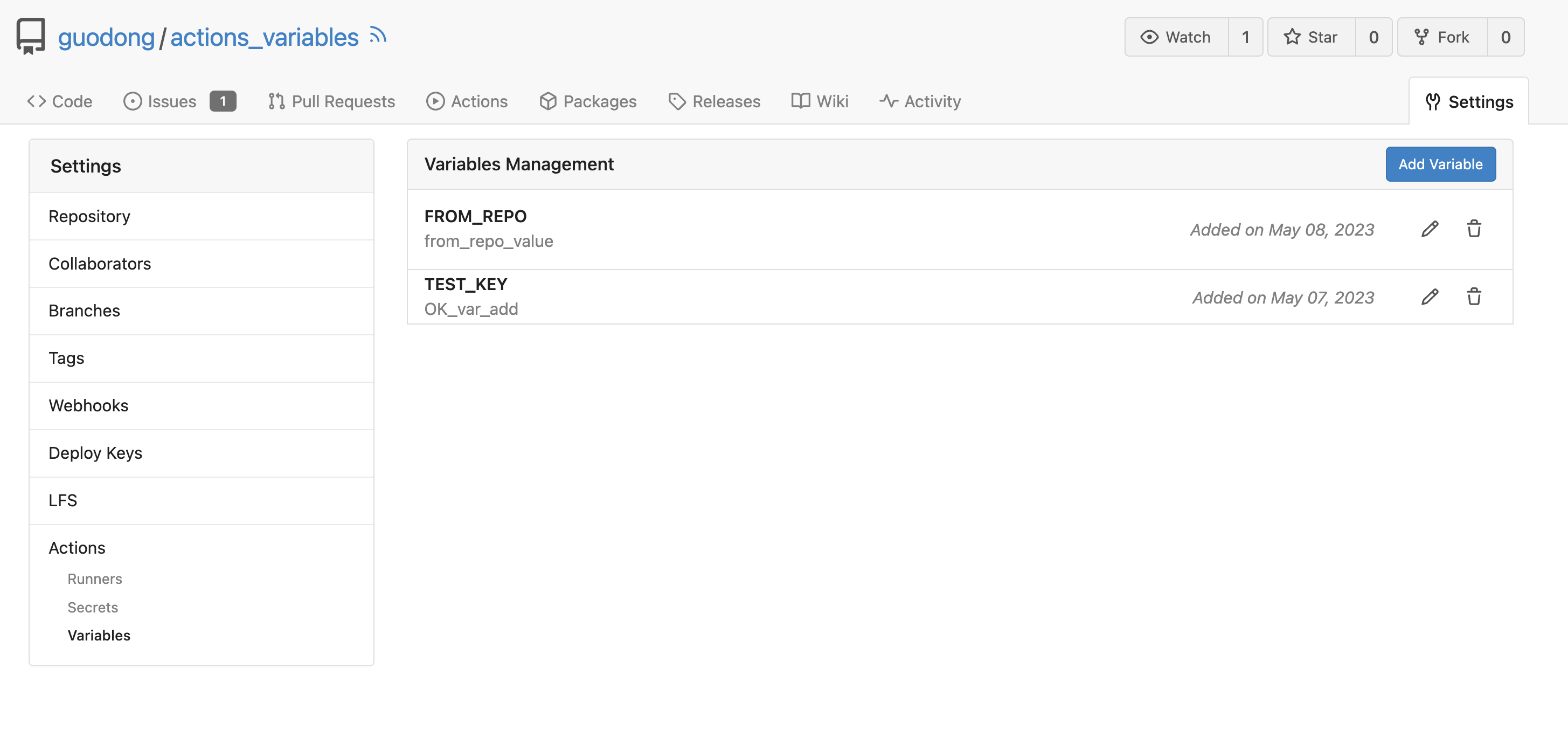 Workflow: ```yaml test_vars: runs-on: ubuntu-latest steps: - name: Print Custom Variables run: echo "${{ vars.test_key }}" - name: Try to print a non-exist var run: echo "${{ vars.NON_EXIST_VAR }}" ``` Actions Log: 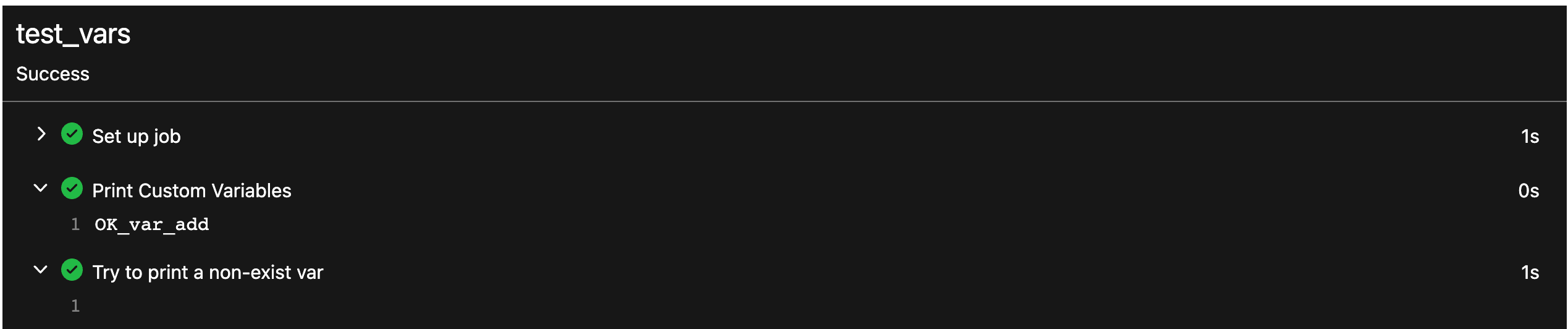 --- This PR just implement the org / user (depends on the owner of the current repository) and repo level variables, The Environment level variables have not been implemented. Because [Environment](https://docs.github.com/en/actions/deployment/targeting-different-environments/using-environments-for-deployment#about-environments) is a module separate from `Actions`. Maybe it would be better to create a new PR to do it. --------- Co-authored-by: silverwind <me@silverwind.io> Co-authored-by: wxiaoguang <wxiaoguang@gmail.com> Co-authored-by: Giteabot <teabot@gitea.io>
129 lines
3.8 KiB
Go
129 lines
3.8 KiB
Go
// Copyright 2023 The Gitea Authors. All rights reserved.
|
|
// SPDX-License-Identifier: MIT
|
|
|
|
package actions
|
|
|
|
import (
|
|
"errors"
|
|
"regexp"
|
|
"strings"
|
|
|
|
actions_model "code.gitea.io/gitea/models/actions"
|
|
"code.gitea.io/gitea/models/db"
|
|
"code.gitea.io/gitea/modules/context"
|
|
"code.gitea.io/gitea/modules/log"
|
|
"code.gitea.io/gitea/modules/web"
|
|
"code.gitea.io/gitea/services/forms"
|
|
)
|
|
|
|
func SetVariablesContext(ctx *context.Context, ownerID, repoID int64) {
|
|
variables, err := actions_model.FindVariables(ctx, actions_model.FindVariablesOpts{
|
|
OwnerID: ownerID,
|
|
RepoID: repoID,
|
|
})
|
|
if err != nil {
|
|
ctx.ServerError("FindVariables", err)
|
|
return
|
|
}
|
|
ctx.Data["Variables"] = variables
|
|
}
|
|
|
|
// some regular expression of `variables` and `secrets`
|
|
// reference to:
|
|
// https://docs.github.com/en/actions/learn-github-actions/variables#naming-conventions-for-configuration-variables
|
|
// https://docs.github.com/en/actions/security-guides/encrypted-secrets#naming-your-secrets
|
|
var (
|
|
nameRx = regexp.MustCompile("(?i)^[A-Z_][A-Z0-9_]*$")
|
|
forbiddenPrefixRx = regexp.MustCompile("(?i)^GIT(EA|HUB)_")
|
|
|
|
forbiddenEnvNameCIRx = regexp.MustCompile("(?i)^CI")
|
|
)
|
|
|
|
func NameRegexMatch(name string) error {
|
|
if !nameRx.MatchString(name) || forbiddenPrefixRx.MatchString(name) {
|
|
log.Error("Name %s, regex match error", name)
|
|
return errors.New("name has invalid character")
|
|
}
|
|
return nil
|
|
}
|
|
|
|
func envNameCIRegexMatch(name string) error {
|
|
if forbiddenEnvNameCIRx.MatchString(name) {
|
|
log.Error("Env Name cannot be ci")
|
|
return errors.New("env name cannot be ci")
|
|
}
|
|
return nil
|
|
}
|
|
|
|
func CreateVariable(ctx *context.Context, ownerID, repoID int64, redirectURL string) {
|
|
form := web.GetForm(ctx).(*forms.EditVariableForm)
|
|
|
|
if err := NameRegexMatch(form.Name); err != nil {
|
|
ctx.JSONError(err.Error())
|
|
return
|
|
}
|
|
|
|
if err := envNameCIRegexMatch(form.Name); err != nil {
|
|
ctx.JSONError(err.Error())
|
|
return
|
|
}
|
|
|
|
v, err := actions_model.InsertVariable(ctx, ownerID, repoID, form.Name, ReserveLineBreakForTextarea(form.Data))
|
|
if err != nil {
|
|
log.Error("InsertVariable error: %v", err)
|
|
ctx.JSONError(ctx.Tr("actions.variables.creation.failed"))
|
|
return
|
|
}
|
|
ctx.Flash.Success(ctx.Tr("actions.variables.creation.success", v.Name))
|
|
ctx.JSONRedirect(redirectURL)
|
|
}
|
|
|
|
func UpdateVariable(ctx *context.Context, redirectURL string) {
|
|
id := ctx.ParamsInt64(":variable_id")
|
|
form := web.GetForm(ctx).(*forms.EditVariableForm)
|
|
|
|
if err := NameRegexMatch(form.Name); err != nil {
|
|
ctx.JSONError(err.Error())
|
|
return
|
|
}
|
|
|
|
if err := envNameCIRegexMatch(form.Name); err != nil {
|
|
ctx.JSONError(err.Error())
|
|
return
|
|
}
|
|
|
|
ok, err := actions_model.UpdateVariable(ctx, &actions_model.ActionVariable{
|
|
ID: id,
|
|
Name: strings.ToUpper(form.Name),
|
|
Data: ReserveLineBreakForTextarea(form.Data),
|
|
})
|
|
if err != nil || !ok {
|
|
log.Error("UpdateVariable error: %v", err)
|
|
ctx.JSONError(ctx.Tr("actions.variables.update.failed"))
|
|
return
|
|
}
|
|
ctx.Flash.Success(ctx.Tr("actions.variables.update.success"))
|
|
ctx.JSONRedirect(redirectURL)
|
|
}
|
|
|
|
func DeleteVariable(ctx *context.Context, redirectURL string) {
|
|
id := ctx.ParamsInt64(":variable_id")
|
|
|
|
if _, err := db.DeleteByBean(ctx, &actions_model.ActionVariable{ID: id}); err != nil {
|
|
log.Error("Delete variable [%d] failed: %v", id, err)
|
|
ctx.JSONError(ctx.Tr("actions.variables.deletion.failed"))
|
|
return
|
|
}
|
|
ctx.Flash.Success(ctx.Tr("actions.variables.deletion.success"))
|
|
ctx.JSONRedirect(redirectURL)
|
|
}
|
|
|
|
func ReserveLineBreakForTextarea(input string) string {
|
|
// Since the content is from a form which is a textarea, the line endings are \r\n.
|
|
// It's a standard behavior of HTML.
|
|
// But we want to store them as \n like what GitHub does.
|
|
// And users are unlikely to really need to keep the \r.
|
|
// Other than this, we should respect the original content, even leading or trailing spaces.
|
|
return strings.ReplaceAll(input, "\r\n", "\n")
|
|
}
|